Always configure SSL for web applications in order to protect session IDs from prying eyes
Set the SSLEnable="true" element to true in the server.xml file
Implement SSL in server.xml

Implement SSL in spring-security.xml by setting force Https property to true

Session Vulnerabilities
- Session hijacking includes exploiting the web session control mechanism that is usually managed by the session token
- In a session hijack attack, the attacker compromises a session by obtaining a session token either through stealing or predicting and gains access to the webserver
- Different ways of compromising a session token are:
– Predictable session token
– Session sniffing
– Client-side attack (XSS, malicious codes, trojans)
– Man-in-the-middle attack
– Man-in-the-browser attack
Types of Session Hijacking Attacks
- Attack using client-side scripting
– Attackers can fix the session ID value by changing the victim’s cookie and inserting a JavaScript code in the URL that will be executed in the victim’s browser
– http://website.kom/document.cookie="sessionid=abcd"; - Attack using <META> tag
– Attackers use code injection attacks by injecting malicious code into the URL and send it to the victim
– http://website.kon/<meta http-equiv=Set-Cookie content="sessionid=abcd"> - Attack through HTTP header response
– An attacker creates a cookie value of the Session ID, modifies the server response and intercepts the packages exchanged between the client and the web application by inserting the Set-Cookie parameter

Types of Session Hijacking Attacks (Cont’d)
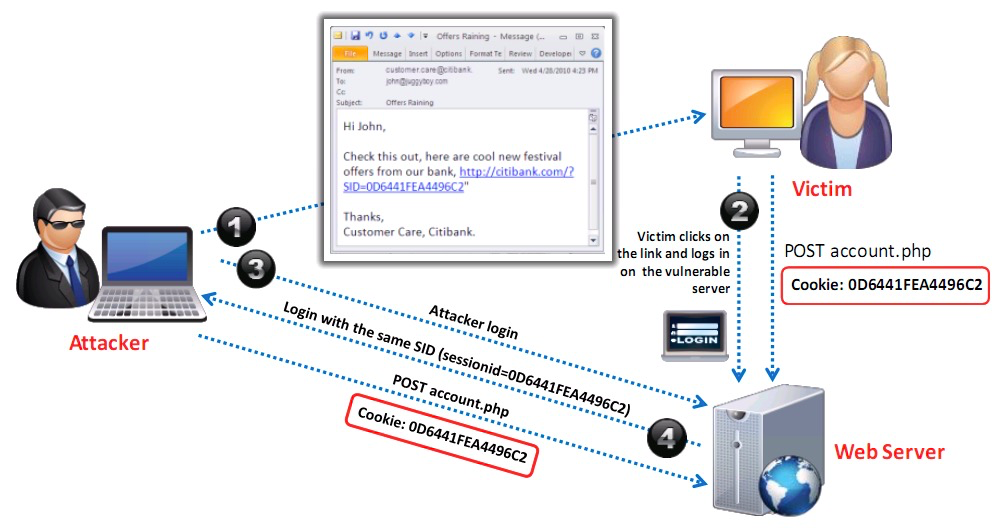
4. Session fixation
– The session fixation attack is a kind of session hijacking, which steals the established session between the client and the web server once the user logs in
– The session fixation attack fixes an established session on the victim’s browser, to begin attack before the user logs in
Types of Session Hijacking Attacks (Cont’d)
5. Stealing session ID through HTTP GET request
– Attackers embed the session ID information in the URL and it is received by the application through HTTP GET requests when the client clicks on the links
– Example: http://wxyz.com/wxyz.jsp?article=1234;session id=ER69045454

