- Session Invalidate
– Session invalidate can be defined as removing the HttpSession object and its values from the system
Example of Session Invalidate

2. Session Validate
– Each session should have a defined timeout when there is no activity
– If needed, a session hard limit can also be used in some cases in order to kill a session irrespective of session activity
– Such settings can be done by either in configuration files or directly in the code itself
Session Validate Sample Code

3. Use POST not GET
– As a part of best practice it is always recommended to use POST instead of GET, as all the major browsers use GET by default for form submission
– In the HTML forms POST should be specified like this <form method ="POST"…>
Vulnerable Code

Secure Code

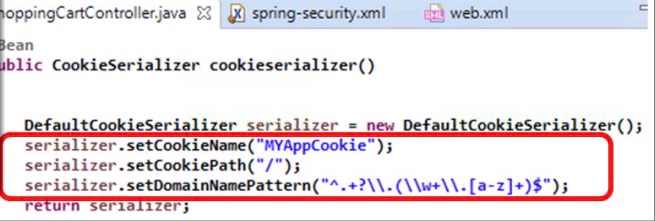
4. Customize the Session Cookie Name, Path and Domain
– As a part of best practice it is always recommended to change the session cookie name from JSESSIONID
– This will protect the cookie from overwriting values from some other application
Vulnerable Code

Secure Code
Configuring Default Cookie Name in web.xml
<session-descriptor><cookie-name>MYWEBAPIID</cookie-name></session-descriptor>
5. Generate a High Entropy Session ID //熵是對某個系統之不確定性或混亂程度的度量方法
– Attackers can guess the session ID if it is of low entropy which is completely predictable
– Generate a complex and less predictable session ID
Vulnerable Code

- If the size of the random key generated and stored is small, it is easy to guess
Secure Code

- This is a complex key which is not predictable
6. Do not Store Non-serializable Objects into a Session
– Non-serializable session objects can not be replicated
– For better reliability and performance it is recommended that session data is serializable
Vulnerable Code

Secure Code

