- Java provides developers with object level protection mechanisms, protecting the integrity and confidentiality of object inside a runtime environment (memory) or that are in transit (stored in IP packets or saved on disk)
- SignedObject class is used for creating authentic runtime objects whose integrity cannot be compromised without being detected
- SignedObject
(jav.security.SignedObject):
– Creates another serializable object (a copy of serializable object)
– Creates in serialized form
– Creates a signature using algorithms (DSA, SHA-1, MD5)
– If the signature is not null then the signed object may contain a valid digital signature
- Signedobjects are used as:
– Unforgetable authorization tokens
– Sign and serialize objects/data
– Verify authenticity of digital signatures
– Construct a logical sequence of signatures
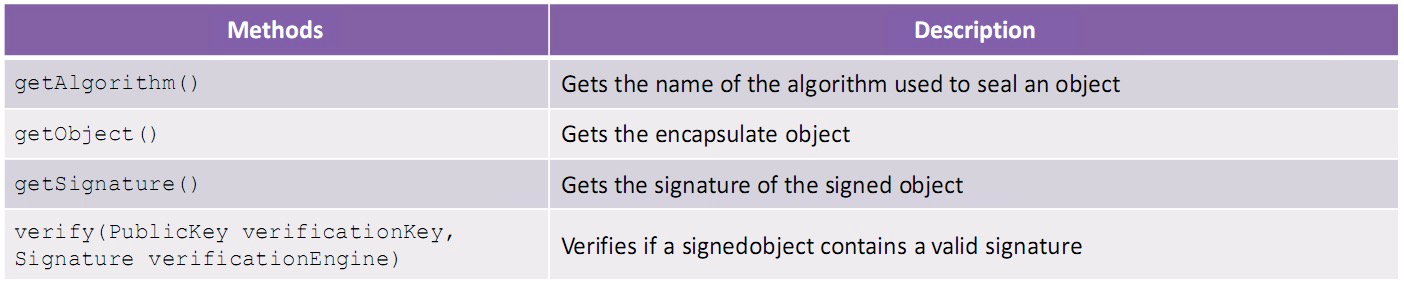
Implementing Methods of SignedObjects
Signing an object
- myobject: The serialized object that needs to be signed
- signingKey: A private key such as DSAPrivateKey, RSAPrivateKey, RSAPrivateCrtKey
- signingEngine: Signature Algorithms can be SHA1withDSA, AES, etc.

Verifying a SignedObject
- publickey: Key used for verification
- verificationEngine: Signature verification engine

The SealedObjects
- Sealedobject class helps developers in creating an object and protecting its confidentiality using cryptographic algorithms
- Sealedobject (javax.crypto.SealedObject)
– Aims at protecting object confidentiality
– Creates serializable object
– Creates cryptographic algorithm (DES, IDEA, RC4)
– Encryption and decryption
– Deserialization of original object - The proper way of maintaining the integrity and confidentiality of Java objects that travel across network is to:
– First, create signedobject
– Second, create sealedobject
Implementation Methods of SealedObject
Encryption

Decryption


